Wazzup Pilipinas!?
In the high-stakes world of cloud security, where a single misconfiguration can spell disaster for global enterprises, one platform stands as a beacon of innovation and reliability. Orca Security has emerged not just as another player in the crowded cybersecurity landscape, but as the definitive solution that's rewriting the rules of how organizations protect their digital assets.
The Game-Changing Promise
Imagine a world where security teams no longer drown in alert fatigue, where every notification carries genuine weight, and where protection spans seamlessly across every corner of your cloud infrastructure. This isn't a utopian vision—it's the reality that Orca Security delivers today.
"Orca alleviates our number one pain: where are our cloud-related security risks? Before Orca, we simply didn't have the visibility I needed," reveals Jonathan Jaffe, CISO of Lemonade, capturing the transformative impact that has made Orca the trusted choice of industry titans.
Beyond Traditional Security: A Platform Built for the Modern Era
Traditional security solutions often feel like using a magnifying glass to examine a skyscraper—effective in isolation but woefully inadequate for the sprawling complexity of modern cloud environments. Orca Security shatters this limitation with its revolutionary approach that treats cloud security as a unified, intelligent ecosystem rather than a collection of disconnected tools.
The platform's genius lies in its comprehensive coverage philosophy. Where competitors force organizations to deploy multiple agents across their infrastructure—creating blind spots, performance overhead, and maintenance nightmares—Orca achieves 100% continuous coverage without requiring a single agent. This agentless approach represents more than just technical innovation; it's a fundamental reimagining of how security should work in the cloud-first era.
The Architecture of Excellence
Orca's Cloud Security Platform operates on three foundational pillars that set it apart from every competitor in the market:
Unified Intelligence Across All Environments
Built as a single, unified platform, Orca eliminates the fragmentation that plagues traditional security approaches. Whether your infrastructure spans AWS, Azure, Google Cloud, Kubernetes, Alibaba Cloud, or Oracle Cloud, Orca provides seamless, consistent protection. This isn't just multi-cloud support—it's multi-cloud mastery.
Lightning-Fast Deployment and Scalability
In a world where "time to security" can mean the difference between protection and breach, Orca deploys in minutes, not months. The platform's patented SideScanning™ technology provides deep visibility into cloud environments without the complexity of traditional deployment models. Organizations can achieve comprehensive security coverage faster than ever before, with the lightweight Sensor available for critical workloads requiring real-time protection.
AI-Powered Intelligence That Actually Works
While competitors tout AI as a marketing buzzword, Orca leverages Generative AI to deliver tangible results. The platform accelerates investigations, streamlines remediation processes, and reduces the skill barriers that have traditionally limited security team effectiveness. This isn't AI for AI's sake—it's intelligent automation that transforms security operations.
The Trust Factor: Validated by Industry Leaders
The most compelling evidence of Orca's superiority isn't found in feature lists or technical specifications—it's written in the success stories of organizations that have transformed their security posture with the platform. From Unity to Autodesk, from Digital Turbine to BeyondTrust, industry leaders across sectors have chosen Orca to protect their most critical assets.
These aren't just customer testimonials; they're validation from organizations that understand the stakes. When Gannett trusts Orca with their media infrastructure, when Hunters relies on the platform for their cybersecurity operations, and when SAP implements Orca across their enterprise software ecosystem, it sends a clear message: Orca Security represents the gold standard in cloud protection.
Comprehensive Protection That Leaves Nothing to Chance
Orca's approach to security coverage is refreshingly thorough. The platform continuously monitors all cloud assets, detecting risks at every layer from infrastructure misconfigurations and vulnerabilities to malware, privileged identities, unsecured sensitive data, API exposures, and AI-related risks. This comprehensive approach ensures that security teams receive the complete picture of their risk landscape, not just fragments.
The platform's strength extends beyond detection to intelligent prioritization. Rather than overwhelming teams with thousands of low-priority alerts, Orca's advanced analytics identify the risks that truly matter, providing detailed contextual data that enables rapid, effective response. This intelligence transforms security operations from reactive firefighting to proactive risk management.
The Compliance Advantage
In today's regulatory environment, compliance isn't optional—it's essential. Orca Security supports over 180 regulatory frameworks and CIS Benchmarks, performing continuous compliance monitoring that can be fully customized for organizational needs. Automated reporting capabilities ensure that compliance status is always current, reducing the burden on security teams while maintaining the highest standards of regulatory adherence.
Cloud-Native Application Protection: The CNAPP Revolution
As organizations embrace cloud-native development, traditional security models become increasingly inadequate. Orca's Cloud-Native Application Protection Platform (CNAPP) consolidates multiple point solutions into a single, powerful platform that includes Cloud Security Posture Management (CSPM), Cloud Workload Protection (CWPP), Cloud Infrastructure Entitlement Management (CIEM), Vulnerability Management, Container and Kubernetes Security, Data Security Posture Management (DSPM), API Security, Cloud Detection & Response, Multi-Cloud Compliance, Application Security, and AI Security Posture Management (AI-SPM).
This comprehensive approach eliminates the complexity and gaps inherent in managing multiple security tools, providing organizations with the unified visibility and control they need to secure their cloud-native applications effectively.
Security Across the Entire Software Development Lifecycle
Modern security requires protection that extends beyond production environments to encompass the entire Software Development Lifecycle (SDLC). Orca delivers this comprehensive coverage through advanced capabilities including Software Composition Analysis (SCA), Static Application Security Testing (SAST), Secrets Detection, Infrastructure as Code (IaC) Security, and Container Image Scanning.
The platform's unique approach traces cloud risks to their origins and provides remediation guidance at the source through its Cloud-to-Dev capabilities, enabling organizations to address security issues before they impact production environments.
The Future of Cloud Security is Here
With over 50 out-of-the-box integrations spanning platforms like Slack, Opsgenie, Jira, and ServiceNow, Orca seamlessly integrates into existing workflows, enhancing rather than disrupting operational efficiency. This integration capability ensures that security becomes an enabler of business objectives rather than an impediment to progress.
Trusted by hundreds of organizations worldwide, Orca Security represents more than just another security platform—it's the foundation upon which modern enterprises build their digital resilience. In an era where cyber threats evolve at the speed of light and cloud environments grow exponentially in complexity, Orca provides the intelligent, comprehensive, and scalable protection that organizations need not just to survive, but to thrive.
Ready to Transform Your Security Posture?
The question isn't whether your organization needs better cloud security—it's whether you're ready to embrace the platform that's defining the future of digital protection. Orca Security offers more than just tools; it provides transformation. More than just coverage; it delivers confidence. More than just security; it enables success.
The cloud security revolution is here, and it has a name: Orca Security. The only question that remains is whether you're ready to join the leaders who have already discovered what next-generation cloud protection looks like.
Ready to experience the difference? Visit orca.security/demo and discover how Orca Security can transform your organization's cloud security posture today.








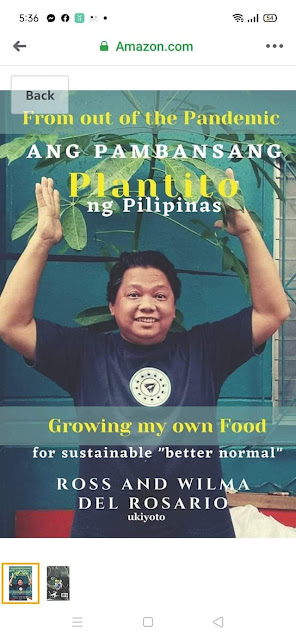
















 Ross is known as the Pambansang Blogger ng Pilipinas - An Information and Communication Technology (ICT) Professional by profession and a Social Media Evangelist by heart.
Ross is known as the Pambansang Blogger ng Pilipinas - An Information and Communication Technology (ICT) Professional by profession and a Social Media Evangelist by heart.











